It’s been always a question , As we are moving to azure cloud environments and Infra & other stuff is manage by MS azure team then how to apply the control & understand the security prospect. Hence azure security center will help you to monitor and give compliance level in border way to not even secure your environments but also adopt the control based on azure security policy. In Security center center you can add your multiple subscription and it will take 24 hrs to collect the data and shows you best recommendation on azure compute, networking storage IOT, Database, webapps & including windows Linux & windows patches level as well. you can enable to File integrity to monitor your file and register level changes etc.
In this Blogs i will be helping to securing the azure environments using the azure security center and witting how to implement the security center to control and apply the rule to meet the compliance level.
Security Center Dash Board will help you to view over all security alerts and Policy compliance View . Subscription been use in the security center etc.
Azure Policy & Compliance : It will help you to assign the security policy in the subscription. Understand what policy and control been applied in this.

Secure Score — Will help you to understand the compliance level based on your score which use the ML/AL algorithm to collect the logs and give your Dashboard view based on ISO-27001, Azure CIS etc Control Report


Click on the Regulatory & compliance Dashboard
you will be able to see the compliance score based on the azure security center policy and Based on the ISO 270001, Azure CIS, PCI, SOC TSP reports .
It’s not mandatory field, To pass the score and but it’s recommended by MS team to get the score & meet the compliance level. Even you can download the report as well.
Apply the controls bases on your organization policy. If you select the specific rules which is non-complainant. Click on the details it will help you get the exact compliance rule and you can fix the compliance level.

If you click on the recommendation. you can see the compliance. It’s shows VMs, Data & Storage ,Networking etc.
Even you can see the IOT compliance as well.

You can add the Azure VMs /On premises VMs while clicking on the Add Computers. you will be able to add the VMs. See the compliance level and can fix the errors.

Click on the networking Tab t understand the security breech or compliance level at Azure networking side.

Data Storage : Click on the Data & storage to get the insight compliance level of SQL DB, Storage , Data Lake & others.

Identity & Access will help you understand compliance level of the Access or any other controls needs to be enable.

If you want to enable the Non-Azure Vms like on-premise you can use the security control solution to get this added. Even it will help you add the SIEM solutions as well.

Adaptive application control is an intelligent, automated end-to-end application white-listing solution from Azure Security Center. It helps you control which applications can run on your Azure and non-Azure VMs (Windows and Linux), It’s helps harden your VMs against malware .
you can enable the adaptive control for the same using below image.

Just-in-time (JIT)- virtual machine (VM) access can be used to lock down inbound traffic to your Azure VMs, reducing exposure to Brute force attacks while providing easy access to connect to VMs.
you can click on the configuration and configure the JIT policy for 3 hrs or 8 hrs access after that it RDP access will revoked automatically for that VMs.

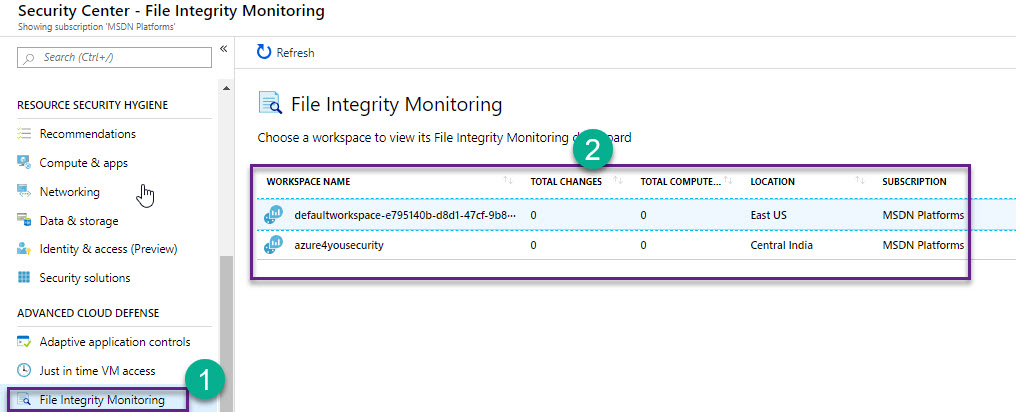
File Integrity Monitoring (FIM), It’s monitor, examines files and registries of operating system, application software. And others for changes that might indicate an attack. A comparison method is used to determine if the current state of the file is different from the last scan of the file. it will help us to comparison to determine if valid or suspicious modifications have been made to your files.
Can be enable the same from the security center.
Custom Alert: You can always configure the custom alerts for your security center based on your organization stranded .

Azure Security Map: Azure Security Map will help you to give the mapping experience. if your azure subscription resources been targeted to attacked and you will know the location for the same.

You can add the automation play book which will help you to fix the issue. when it’s arias or based on the organization standard you can have you set of rule can be leveraged with Play Book.



Leave a comment